Logs
This section explains the log reports available within the Admin Interface. The following topics are covered in this section:
Viewing logs
Log information provided on this page is split into events that occur against the different Osirium PAM service types. Each tab contains information for a specific service, allowing you to easily target your search.
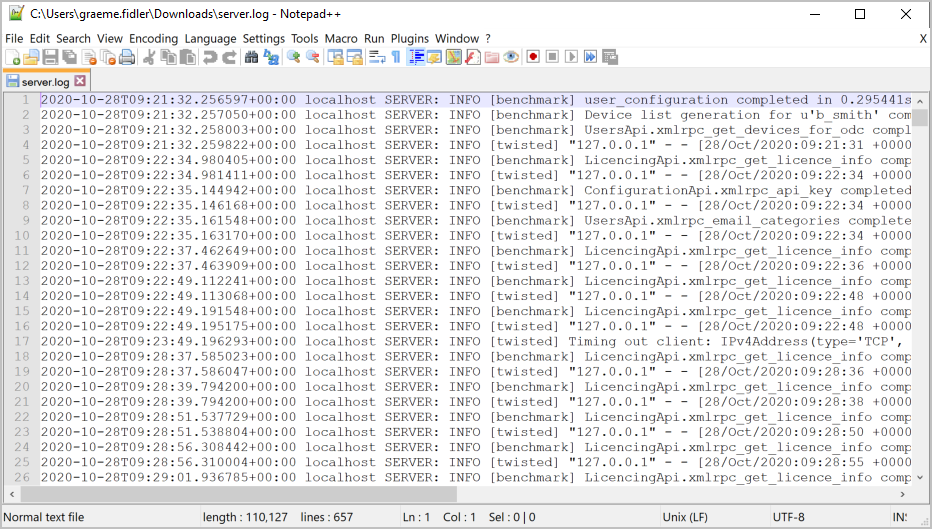
Logs can be downloaded for each individual tab using the DOWNLOAD button. The downloaded file is saved as something.log on your local workstation and can be viewed in an external text editor.
The following is a view of the Server log tab.

The following is a view of the Server log downloaded and viewed in an editor.
The following describes each log and what they contain, to help you pinpoint the right log when troubleshooting issues.
| Heading | Description |
|---|---|
| Server | Logs from the Server service which handles the XML remote procedure calls (RPC) from the Admin Interface and loads device templates, when device tasks are being executed. |
| Proxy | Logs from the Proxy service, which handles the connections between the user's workstation to the end device, when a device is accessed. It's responsible for injecting the authentication requirements to enable the user to connect to the device. |
| Proxy Channels | A log of all successful proxy connections with corresponding channel IDs. Proxy connections act as the middle-man throughout the connection life cycle, so users never have to know the device login credentials. |
| RDP Proxy | Logs from the RDP Proxy service, which handles proxying of connections to RDP devices, capable of credential injection and RDP channel blocking. RDP Proxy supports RDP connections to Windows Server 2003 and newer. |
| External | Logs from the External service, used to authenticate the user logging on and produces the device and task list the user has permission to. Any device permissions are dynamically published and device monitor states updated. This service will also manage the authentication for users that are authenticated against configured identity providers. |
| Userauth | Logs from the Userauth service, which handles user login attempts and failures based on the users auth type (local, RADIUS, Active Directory, multi-factor or SAML). |
| Cluster | Audits the cluster, logs nodes joining the cluster and displays cluster errors. |
| Rest | Logs from the Rest service, which handles requests and receives responses via HTTP protocols. |
| HA proxy | Logs from the HA Proxy service, which manages and provides load balance high availability of device connections. |
| Session recording | Logs from the SessionRecording service, which receives screenshots sent from the user sessions, stores them and creates a database record for each. |
| Task tracker | Logs from the TaskTracker service, which maintains an accurate record of the system tasks that are run in the background. |
| MAP Server | Logs from MAP services, which include MAP sessions and which device template script was used. |
| Key Verifier | Logs from the Key-Verifier service, which verifies fingerprints associated with a device when a connection is made to a device tool. |
| API | Logs from the Rest-API service, showing all the API calls that are made, the client that made the call and which API call was used. API logs can be found in: /var/log/osirium/rest-api.log . |
| SMTP Email | Logs listed are from the SMTP debug log file. They log the communication between Osirium PAM and the configured SMTP server. Shows any issues with sending emails through error messages that come back from the SMTP server. |
| UI Session | Logs from the UI Session Manager service, logging related to logins and logouts via the UI. |
| UI API | Logs from the UI Rest API service, including issues related to Rest API calls made from the UI. |
| UI Device | Logs from the UI Device service, showing logs associated with the device tool connections i.e. RDP, SSH made. |
| UI Session Recording | Logs from the UI Session Recording service, showing logs relating to received screenshots taken during the connection through the UI. |
| UI Socket.io | Logs from the UI Socket.io service, including logs related to the socket.io communication between the UI clients and Osirium PAM. |
| SAML2 | Logs showing records of SAML logins and configuration changes to the SAML service. |
Logging levels
The Osirium PAM event occurrences are given a logging level of either: Debug, Info, Warning, or Error.
The table below describes when logging is used:
| Level | Description |
|---|---|
| Debug | Provides detailed information to help with diagnosing problems By default debugging is turned off. To enable the debug logging mode see Debug Task Logging. |
| Info | Information to confirm that the service is working as expected. |
| Warning | Gives an indication that something unexpected happened. The service is still working as expected but something to be aware of. |
| Error | Indicates an exception has occurred and there maybe a problem. |
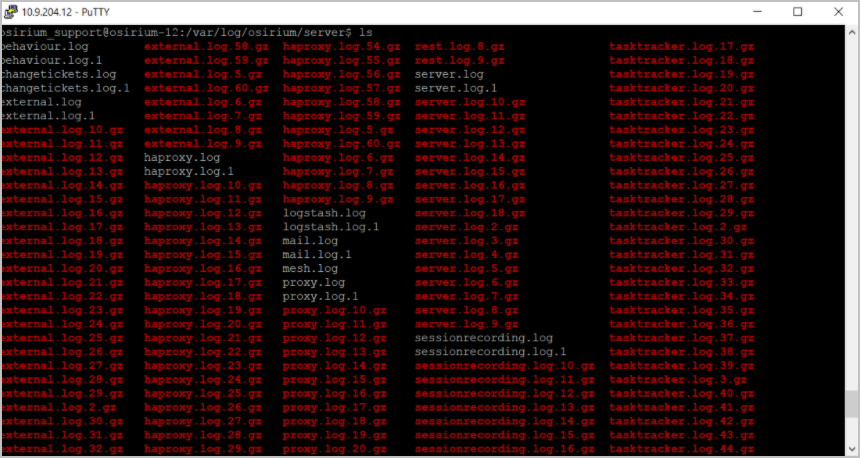
Log file directory
All log files are stored in plain text on the virtual appliance local filestore and can be found in the /var/log/osirium/server directory. They can be accessed using a BASH command and logging in as the osirium_support account. See Support Account.
Logs are rotated automatically once a day and kept for a maximum of 84 rotated logs, after which they are deleted. Rotated logs are archived as compressed GZ files.
The following is an unfiltered view of the log files found in the /var/log/osirium/server directory.
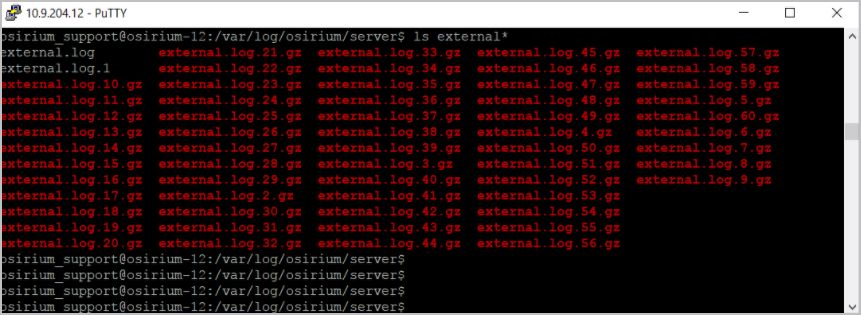
The following is a filtered view for the external log files found in the /var/log/osirium/server directory.
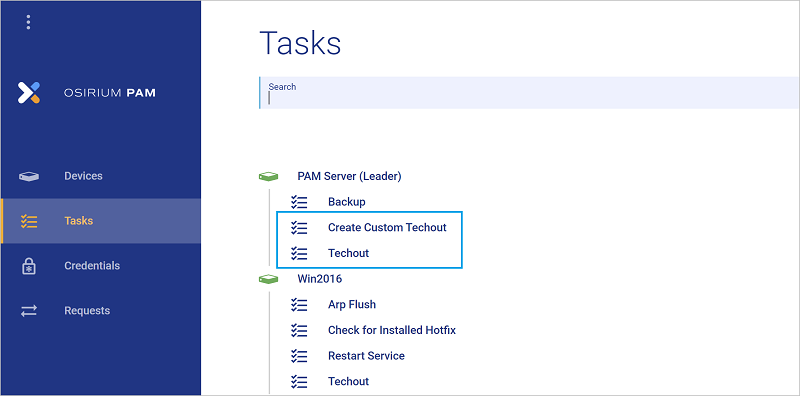
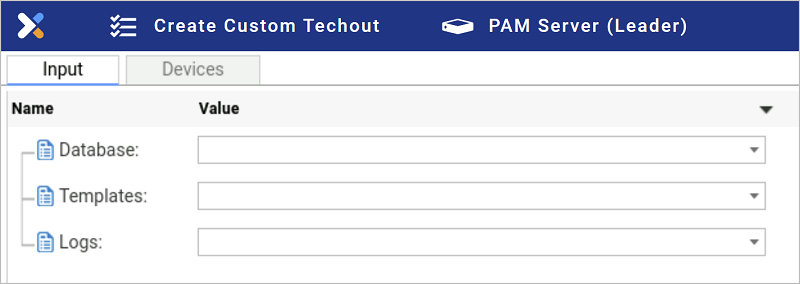
Log file techout
A techout is a TGZ archive file that gathers system and configuration information. A techout task can be run against the PAM Server which will include all the log files. Alternatively, you can create a custom techout which will allow you to select:
- Include all: which will include logs that are up to 84 days old.
-
Include recent: which will only include logs that are 10 days old.
Troubleshooting
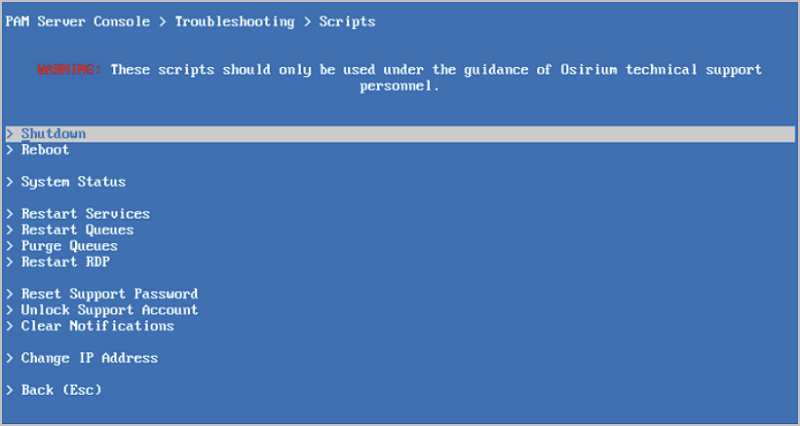
A number of troubleshooting scripts are available through the PAM Server console screen to help you manage system and service tasks.
To view the console window:
-
Logon to your existing infrastructure and open the console window of the PAM Server.
-
Within the blue screen console window, select
Troubleshooting.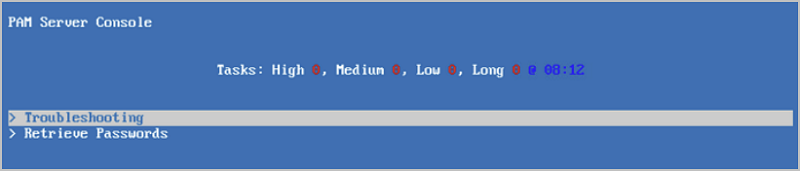
-
Now enter the username and password of a SuperAdmin account.
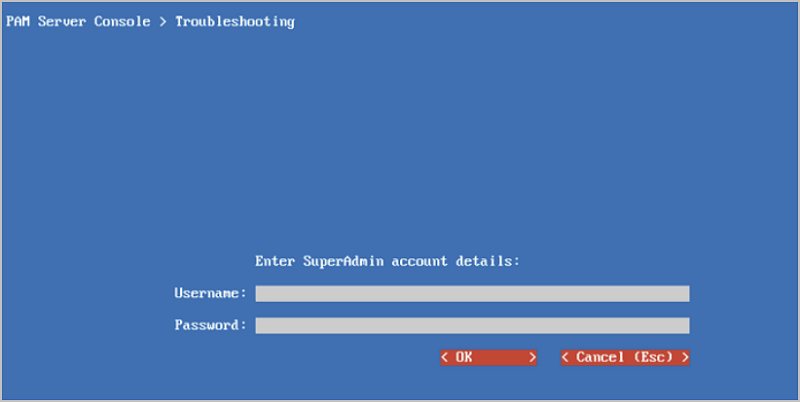
-
You will now see the list of troubleshooting scripts. These are the tasks that can be run on the server to help resolve issues.