Managing devices
This section describes how devices are provisioned and managed within the Admin Interface. The following topics are included in this section:
- Manage devices
- Control accounts
- Device Discovery
- Adding a device
- Adding a device using a local device Account
- Adding an Active Directory member device using an Account Source
- Adding a device using a static vault Account source
- Bulk importing
- Unprovision
- Force remove
- Device detail page
- Configuration tab
- User access control tab
- Account management tab
- Create a local account on a device
- Tasks tab
- Migrating a template
- Trigger Audit
- Editing a device
Manage devices
The manage devices page provides a list of all devices provisioned in Osirium PAM. A device template is required to provision a device so it can be administered.
Device templates provide Osirium PAM with the necessary access control and account provisioning information for a device. Device templates can be expanded to include auditable parameters, delegated tasks and custom business process tasks. See Template Library.
To provide device access to users, profiles need to be created and devices, tools, tasks, users, user groups added to the profile. See Creating a New Profile.
To view the Manage devices page, click Devices in the left-hand menu.
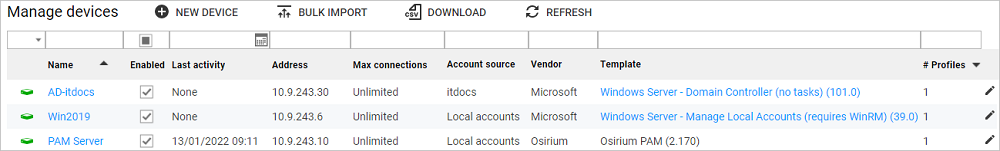
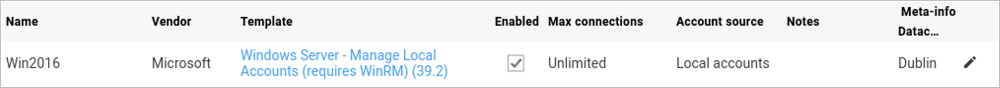
The information presented in the table includes:
| Heading | Description |
|---|---|
| Device status icon | The following describes what the different device icon states mean: |
| Name | This is the display name that will be given to the device, to identify it within the UI and Admin Interface. |
| Enabled | If the checkbox is  checked then the device is enabled. Allows the user to access the device. checked then the device is enabled. Allows the user to access the device.If the checkbox is |
| Last activity | Represents the date and time the device was last accessed.. |
| Address | The the network IP Address of the device. |
| Max connections | Allows you to set a maximum limit for the number of connections or users that can be connected to the device at any one time. - For RDP and SSH the maximum connections refers to the maximum number of connections to the device. - For HTTP/HTTPS connections the maximum connections refers to the maximum number of users. This is because the proxy cannot determine how many separate HTTP/HTTPS sessions a user has open to the device. Leaving the field blank defaults to unlimited connections. NOTE This functionality is useful in cases when you: - Have device license limits. - Want to restrict the number of users that connect to a device. |
| Account source | Indicates which account source method the device is using. See Active Directory or see Manage Static Vaults. |
| Template | Name and version of the device template that is being used to manage the device. See Template Library. |
| Vendor | Name of the device vendor. |
| # Profiles | Displays the number of profiles the device belongs to. |
| Meta-info | Meta-columns allow you to attach many kinds of information against each device. For details on configuring meta columns, see Configure Meta-Info. |
Device context menu options
A number of context menu options are available when you highlight a device and then right-click. Some of the more common options are described in the Common Interface Functions section.
| Action | Description |
|---|---|
| Clear alert | Once the alert has been investigated and resolved, the alert can be cleared by the using this option. The MonitorDevices task and Lower Alert task is run against the device. If there have been no more failed tasks, then the device status will be set to  . . |
| Migrate template | Allows you to migrate the device to a different template. See Migrating a Template. NOTE You can't migrate the template of a device which has been disabled. |
 Unprovision Unprovision |
Unprovisioning a device removes the device so it can no longer be administered. See Unprovision. |
 Force remove |
Deletes the device without attempting to delete any Osirium PAM accounts from the device or Active Directory. Used in cases where the device has been taken off the network and will not be reinstated. NOTE Caution should be used if the device is still functional. If the device has been provisioned as Managed, then you will have to change the password. To recover the password you must generate a breakglass KeePass file so you have the password to log onto the device directly. See Generate Breakglass KeePass File. |
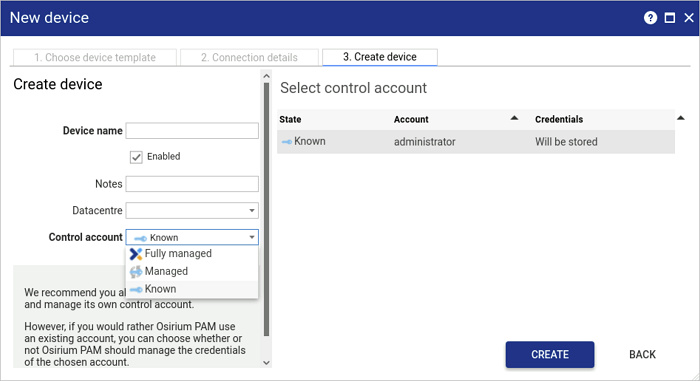
Control accounts
When provisioning a device, the user has a choice as to how the device will be managed. The following diagram explains the control account options available when provisioning a device.
| On Osirium PAM | On Device | |
|---|---|---|
| Control Account Type | Store Password | Change Password |
| Known |  |
|
| Managed |  |
 |
| Fully Managed |  |
 |
Device Discovery
An easy way to provision devices is to use the device discovery task available through our PPA product. PAM's collaboration with PPA allows the automation of device discovery and provisioning of devices within PAM.
Using the PPA device discovery task will allow you to:
- Reduce workload for administrators
- Automatically discover devices on your network to make sure you capture them all
- Save time through automated bulk provisioning of devices in PAM
- Quickly configure privileged access to users within the same task
- Run adhoc or as a schedule to capture any new servers coming online
Limitations
Active Directory devices only: The device discovery playbook will only support the provisioning of devices with a template that has an account source of Active Directory. The default will be the Windows Server template. To use a different template the playbook will need to be edited.
Account mappings only: When PPA adds the device to a profile, the device access level can only be set to a mapped account but can be changed later through the PAM Admin Interface.
For further information and setup information see here.
Adding a device
There are a number of ways Osirium PAM can interact with devices:
-
Adding a local device: Osirium PAM creates/uses a local account on the device. If a local account with an Account state of Fully Managed is used, Osirium PAM will create two management accounts on the device. These accounts will be used to communicate with the device, execute commands and runs tasks on the device.
-
Adding a device using an Active Directory: Osirium PAM uses an existing Active Directory account with the correct privilege level to perform the required task.
-
Adding a device using an account listed in the static vault: an account is selected from accounts stored within Osirium PAM static vault service. These accounts are pre-existing on the device being provisioned.
Adding a device using a local device account
To add a device using an account that already exists on the device:
-
On the Manage devices page, click on the

NEW DEVICEbutton. The New device window opens. -
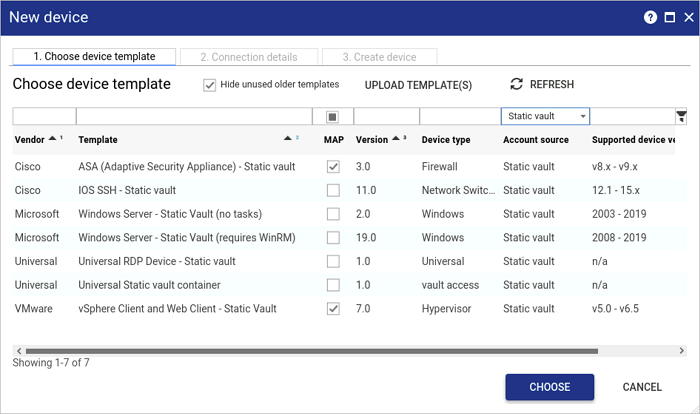
In the Choose device template window, click on the correct template for the device.
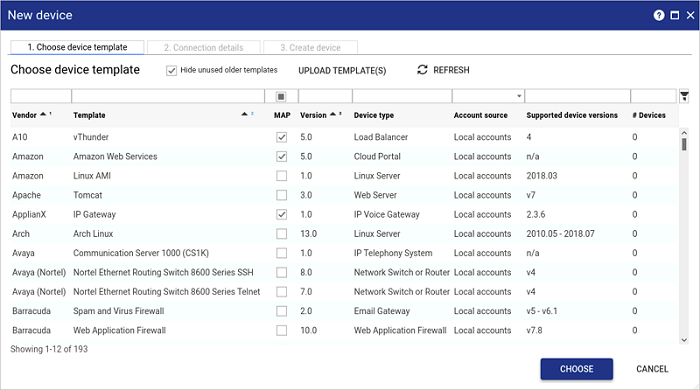
-
Click
CHOOSE. -
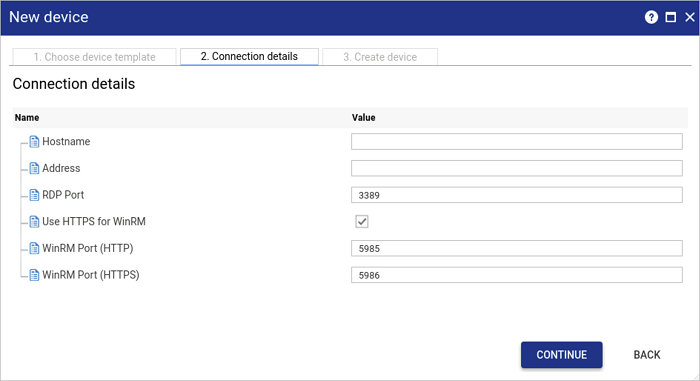
In the Connection details window, enter the device configuration information which will be used to make a connection.
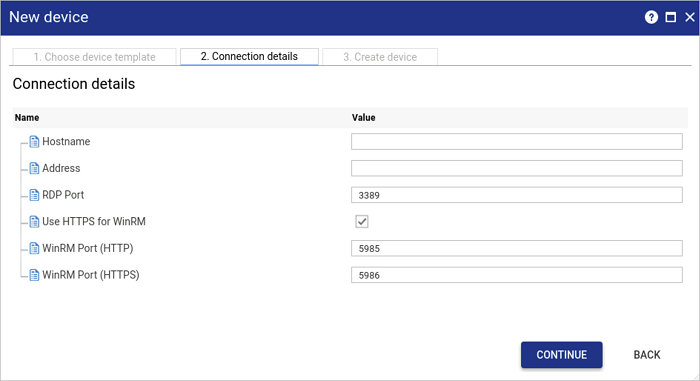
Note
The fields within the Connection details page may differ depending on the device template selected.
To validate the hostname use the following naming convention:- First character: alphanumeric (A-Z a-z 0-9).
- Middle character(s): alphanumeric (A-Z a-z 0-9) and dash (-).
- Last character: alphanumeric (A-Z a-z 0-9). -
Click
CONTINUE. The Device access details window appears.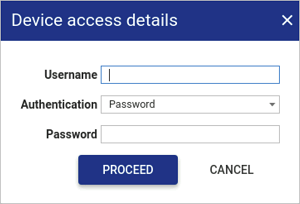
-
Within the Device access details window, enter a valid device account username.
-
In the Authentication drop-down, select one of the following authentication methods:
- Password: provisions the device with a password only.
- SSH Key: provisions the device with SSH key authentication only.
- Both: provisions the device with both SSH key and password authentication.
Depending on your selection, one or more credential fields display beneath the Authentication drop-down.
-
In the available field(s), provide the authentication credentials:
- Password: type a password.
- SSH private key: click the field or
 to upload an SSH private key.
to upload an SSH private key. - SSH key passphrase: if necessary, type an SSH key passphrase.
-
Click
PROCEED. The Device Verify Task is run:- Osirium PAM uses the credentials provided to connect to the device.
- Checks the device version is compatible with the template selected.
- Closes the connection to the device.
Note
At this stage, the device account details provided are not stored within Osirium PAM. They are temporarily stored in your browser as they will be required again later.
-
In the Create device window, on the left-hand side, enter a Device name to help identify the device.
-
Select a control account state. The state selected will determine how the selected account will be managed. See Control Accounts.
The selected control account will be used to:
- Create and delete Osirium PAM accounts on the device.
- Run tasks on the device.
- Refresh passwords.
-
Click
CREATE. The control account is used to communicate with the device and runs the following tasks to complete the provisioning:DeviceAudit task:
- Audits the device and gathers the relevant information to populate the Inventory report.
- Discovers any local user accounts and assigns an account state to each account.
If any known accounts have been specified in the template, they will be audited and assigned a state of Approved. All other device accounts found during the audit will have a state of Unapproved. See Changing States.
DeviceProvision task:
Depending on the control account state selected the following operations will be performed:
Control accounts Description Fully managed Uses the devices access details provided within the Connection details tab to create an Osirium PAM management account (osirium1) on the device. This account will be given the highest access level available on the device. The device access details provided will NOT be stored.
The newly created Osirium PAM management accounts will be used to manage and run tasks on the device.
Managed Uses the devices access details to connect to the device. The selected control account name is stored and it’s password changed. The control account password with be managed and Osirium PAM will use this account to manage and run tasks on the device.
Known Uses the devices access details to connect to the device. The supplied username and password is stored in the database.
The account will be used to manage and run tasks on the device.
Adding an Active Directory member device using an account source
Osirium PAM can interact with the Active Directory directly to offer the same range of single sign-on options that you have with a device with local accounts.
Adding member servers:
-
Before member servers/clients can be provisioned using an Active Directory account source, the Active Directory must first be added. See Adding an Active Directory.
-
On the Manage devices page, click on the

NEW DEVICEbutton. The New device window opens. -
Click a template requiring an Active Directory account source.
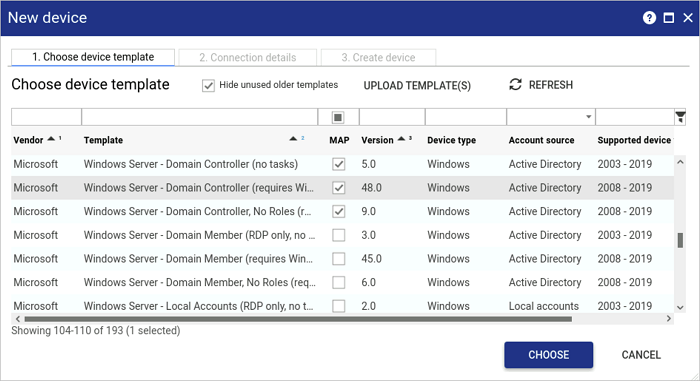
-
Click
CHOOSE. The Connection details window appears. -
In the Connection details window, enter the member servers/client configuration information which will be used to make a connection.
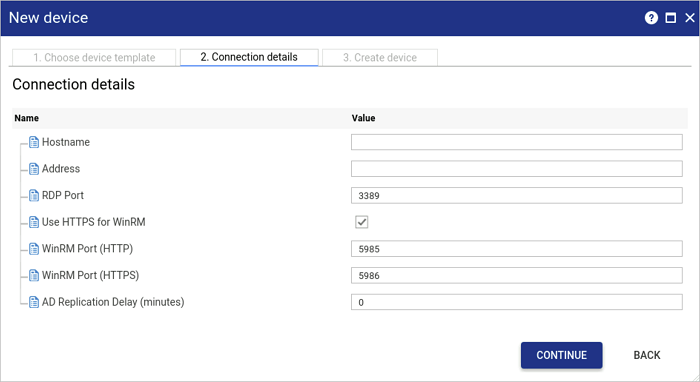
Note
Active Directory Replication delay is available for Active Directory domains with multiple sites that may be using inter-site replication delay.
For example:
- An Active Directory domain has a Site A and Site B.
- The inter site replication delay between these two sites is 15 minutes.
- If a new group is added into Active Directory on the Domain Controller in Site A, it would take 15 minutes for the group to be replicated to Site B.
- This means that if the account source is the Domain Controller on Site A, and a member server from Site B is provisioned, then the task would fail until the replication has taken place. -
Click
CONTINUE. -
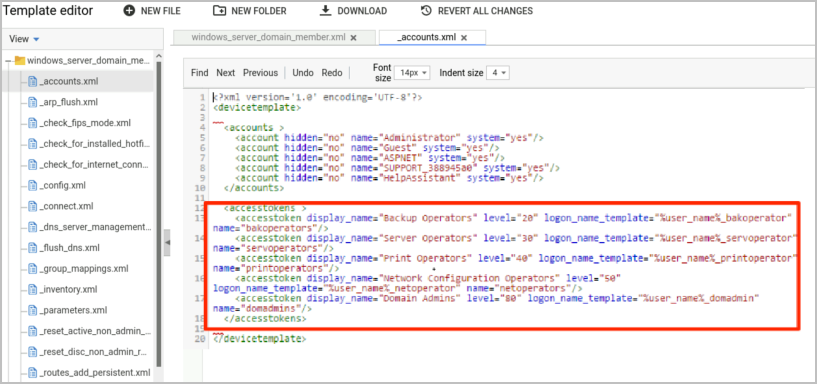
In the Create device window, select a control account from the accounts listed which exist on the Active Directory, but not on the member servers. See Control Accounts.
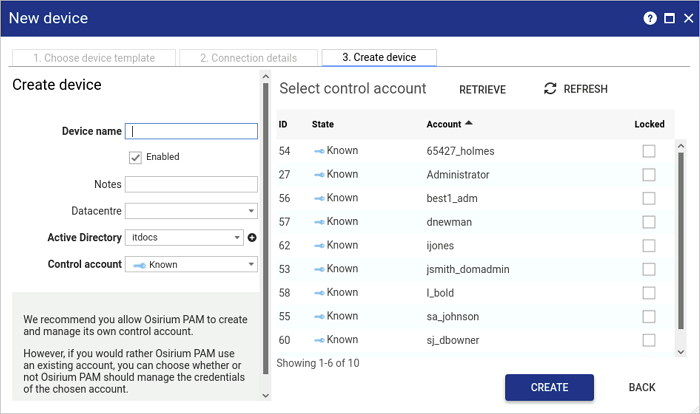
-
Click
CREATE. The member servers provisioning process will be queued and perform different operations depending on the type of control account selected.The DeviceAuditTask is run:
- The control account is used to audit the accounts that exist on the Active Directory and the accounts that exist on member servers/client.
- If any known accounts have been specified in the template using the
<accounts>tag, they will be listed on the Manage accounts page and the Device detail > Account management tab, with a state of Approved. - All other Active Directory accounts found during the audit will have a state of Unapproved.
The DeviceProvisionTask is run:
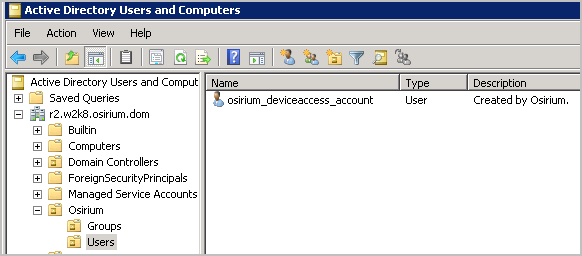
- Osirium PAM uses the Active Directory details provided during connection to create the osirium_deviceaccess_account on the Active Directory within the Osirium OU > Users OU. This account will be used to manage the member servers.
- The selected Active Directory account is NOT stored in Osirium PAM.
-
The osirium_deviceaccess_account account will be marked as the control account on the Manage accounts > Service accounts tab and linked to the user: PAM Server.
-
Osirium PAM uses the control account.
-
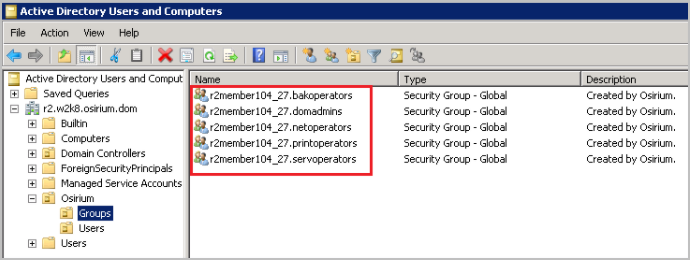
The Group OU is created within Osirium PAM OU on the Active Directory, and a group per accesstoken (derived from the template) is created. Each accesstoken is then added as a member of the appropriate built-in group in Active Directory.
Note
The osirium_deviceaccess_account may already have been created when the Active Directory was added, if the create account checkbox was checked.
Adding a device using a static vault account source
To provision a device to use an account store in the static vault:
-
Before a device can be provisioned ensure the account has been added to the static vault. See Manage Static Vaults.
-
On the Manage devices page, click on the

NEW DEVICEbutton. The New device window opens. -
Click a template requiring a static vault account source.
-
Click
CHOOSE. The Connection details window appears. -
In the Connection details window, enter the device configuration information which will be used to make a connection.
-
Click
CONTINUE. -
In the Create device window, select a static vault. The Select control account window will update and list all the accounts available in the selected static vault.
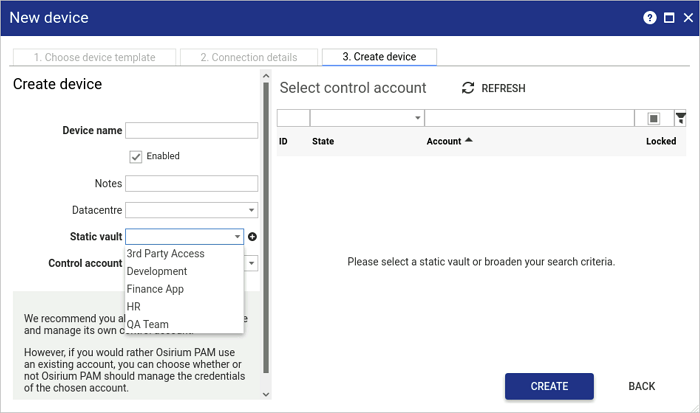
-
Select an account from the list.
-
Click
CREATE. The device will be provisioned.The control account selected will be used to:
- Create and delete Osirium PAM accounts on the device.
- Run tasks on the device.
- Refresh passwords.
-
The DeviceAudit task is run:
- The control account is used to audit the accounts that exist on the device and populate the Inventory report.
- If any known accounts have been specified in the template using the
<accounts>tag, they will be listed on the Manage accounts page and the Device detail > Account management tab, with a state of Approved. - All other device accounts found during the audit will have a state of Unapproved.
The DeviceProvisionTask is also run during the provisioning process. As all static vault accounts are known, Osirium PAM uses the devices authentication details stored in the static vault to connect to the device.
Bulk importing
Devices can be bulk provisioned with the bulk import feature. You can download a preformatted CSV (comma separated value) for each device template and populate it with the relevant data.
To bulk import devices:
-
On the Manage devices page, click

BULK IMPORT. -
Within the Import from CSV window opens, click
DOWNLOAD CSV TEMPLATE. -
Within the Bulk import template download window, click on a device template to download the appropriate bulk import template.
-
Click
DOWNLOAD BULK IMPORT TEMPLATE. The CSV file downloads to your default download location.If the PAM Server Browser (HTTP) tool is being session recorded, then you will need to use the Shared Drive mechanism for downloading files. For further details see Downloading a file using Shared Drive.
-
Open the downloaded bulk import template and populate. The bulk import template may vary depending on the template selected.
Some of the common fields may include the following:
Column name Description Vendor
Template
VersionThe device template information has to match a template which has been uploaded into Osirium PAM. You can find this information on the Template library page. See Template Library
Name This is the display name that will be given to the device, to identify it. Username Enter the name of a valid device account. This account will be used to access and provision the device. NOTE For a Windows member server, leave blank as the Active Directory account details will be used.
Password Enter the password of the device account used. NOTE For a Windows member server, leave blank as the Active Directory account details will be used.
Control account Enter one of the following options depending on how you want to manage your device.
- Fully managed
- Managed
- KnownSee Control Accounts.
Control username This field is only required if the control account selected is either Managed or Known. This is the account that will be used to communicate with the device. Control password This field is only required if the control account selected is either Managed or Known. This is the account password that will be to communicate with the device. Account source Required for devices using an Active Directory or static vault account source. If using Active Directory, enter the name given to the Active Directory in Osirium PAM.
If using a static vault, enter the name given to the static vault in Osirium PAM.
Hostname Is the unique label assigned to the device which is used internally to identify the device. Address Is the network IP address of the device. Other columns This may vary depending on the device. Meta-cols Meta-columns allow you to attach many kinds of information against each device. See Control Accounts. -
Savethe file. -
Now within the Import from CSV window, click
Choose File.If the PAM Server Browser (HTTP) tool is being session recorded, then you will need to use the Shared Drive mechanism for uploading files. For further details see Uploading a file using Shared Drive.
-
Click
IMPORT. -
The entries in the CSV file are added and visible in the Bulk import devices window.
-
Before you click
IMPORTnote the following.-
If a template contained in the imported file is not found in the Template library, a warning window will be displayed. Check that the details entered in the Vendor, Template and Version fields match a template in the Template library.
-
To import all the devices listed, click the

SELECT ALLbutton. -
To import only a selection of devices from the list, hold the CTRL key and select the devices you want to import from your bulk import list.
-
Errors will be highlighted with a warning icon.
-
If warnings are not fixed then you will get an error when you click
IMPORT. You can select the Skip rows with errors to ignore the entires with errors and import all the others. -
You can select the Reprovision existing devices to reprovison any existing devices.
-
You can update any device settings by clicking on the
 at the end of each row.
at the end of each row. -
If there are no errors highlighted then all users will be imported in the list.
-
To set the username and password to a valid device account for all the devices listed, click the

SELECT ALLbutton and then click theAPPLY USER/PASSbutton. -
To set the username and password to a valid device account for only a selection of devices, hold the CTRL key and select the devices and then click the
APPLY USER/PASSbutton.
-
-
Click
IMPORT. -
Within the Question window, click
YESif you are happy to proceed with the bulk import. -
Within the Action queue window, devices will be imported and queued for creation. If you have a lot of devices in your bulk import then you can choose to
Continue in the backgroundor if the imports have been completed, clickDONE.The Manage devices page will automatically be updated.
Unprovision
Unprovisioning a device removes the device so it can no longer be administered.
To unprovision a device:
-
On the Manage devices page right-click on a device and select

Unprovisionwithin the context menu. -
If the device belongs to a profile:
- In the Action notification pop-up, click
CONTINUE. - You will be asked to supply new credentials for any accounts on the device which are in the Managed state. Alternatively, you can click
BULK APPLY, which will apply the same credentials to all the accounts. - Click
PROCEED. The Refresh Account Credentials task is run to set the new credentials on the accounts on the device.
- In the Action notification pop-up, click
-
Within the Question window, click
YES, if you are sure you want to delete the device.
During the deletion of the device the following occurs depending upon what the control account is set to:
UserDeviceAccountUpdateTask is run:
- Before the device is unprovisioned and automatically removed from all profiles. This allows all Fully managed user accounts to be deleted from the device or the Active Directory if unprovisioning member servers.
DeviceUnprovisionTask is run:
-
Fully managed
- Connection to the device is made using the osirium1 management account and deletes the osiriumbg account. Applies to local devices only.
- The management account osirium1 will also be deleted if the device allows. Applies to local devices only.
- Removes the device information from Osirium PAM, i.e. Manage devices, Inventory, Manage accounts, etc.
-
Managed
- The Managed control account is NOT removed from the device.
- Any Windows Member accesstokens are deleted from the Group’s OU on the Active Directory. Applies only to member servers.
- Removes the device information from Osirium PAM, i.e. Manage devices, Inventory, Manage accounts, etc.
-
Known
- The Known control account is NOT updated or removed from the device.
- Any Windows Member accesstokens are deleted from the Group’s OU on the Active Directory. Applies only to member servers.
- Removes the device information from Osirium PAM, i.e. Manage devices, Inventory, Manage accounts, etc.
Force remove
Devices which are stuck in an unprovisioned state  can be removed by right-clicking a device or selecting multiple devices on the Manage devices page and then clicking
can be removed by right-clicking a device or selecting multiple devices on the Manage devices page and then clicking 
Force remove from the context menu.
Force remove will delete the device without attempting to delete Osirium PAM accounts on the device.
For member servers, force remove will delete the Windows Member without attempting to:
- Delete Osirium PAM accounts from the Active Directory.
- Delete the Windows member accesstokens within the Group’s OU on the Active Directory.
This approach can be used in cases where the device has been taken off the network and will not be reinstated.
Note
Caution should be used if the device is still functional. If the device has been provisioned as Managed, then you will have to change the password. You will be asked to provide a new password and attempt to change the password on the device.
If the password reset fails, you can recover the password set by using the Reveal Credentials tool or generating a breakglass KeePass file so you have the password to log onto the device directly.
Device detail page
The Device detail page provides information relating to the device and allows you to administer the device.
To view the Device detail page, click on a name within the Name column which is a link to the Device detail page. Alternatively, highlight a device and right-click for the context menu. Within the context menu select 
Show and you will be navigated to the Device detail page.
The Device detail page contains the following tabs:
- Configuration tab.
- User access control tab.
- Account management tab.
- Tasks tab.
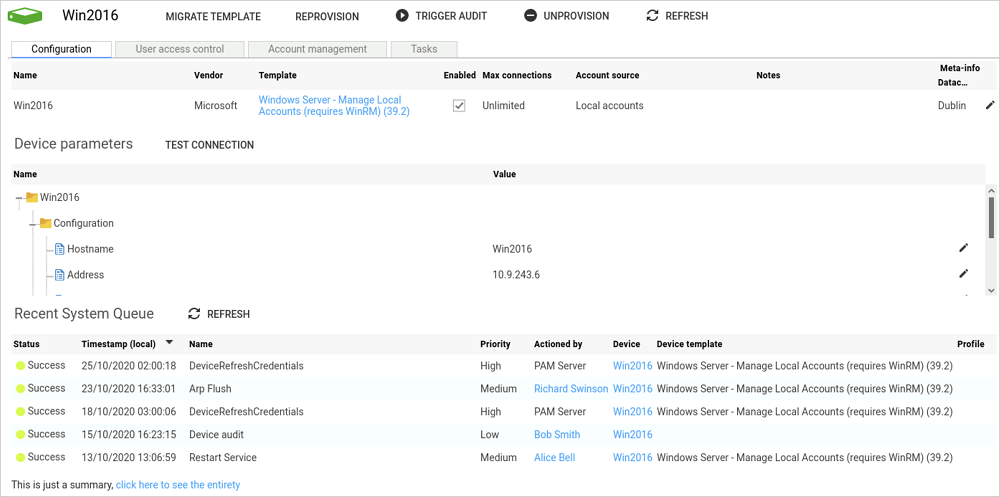
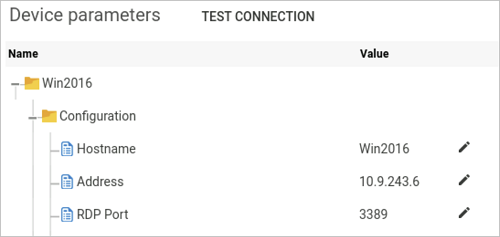
Configuration tab
The Configuration tab allows you to view and manage the internal device information and device parameters which are used to communicate with the device.
Internal device information
This information is used to identify the device. Click on the  icon at the end of row to edit the saved information.
icon at the end of row to edit the saved information.
Device parameters
This information is essential for Osirium PAM to be able to connect to the device. Click on the  icon to configure the Hostname, IP address and other device configurations.
icon to configure the Hostname, IP address and other device configurations.
If changing these parameters, use the TEST CONNECTION button to confirm that the PAM Server can still connect to the device.
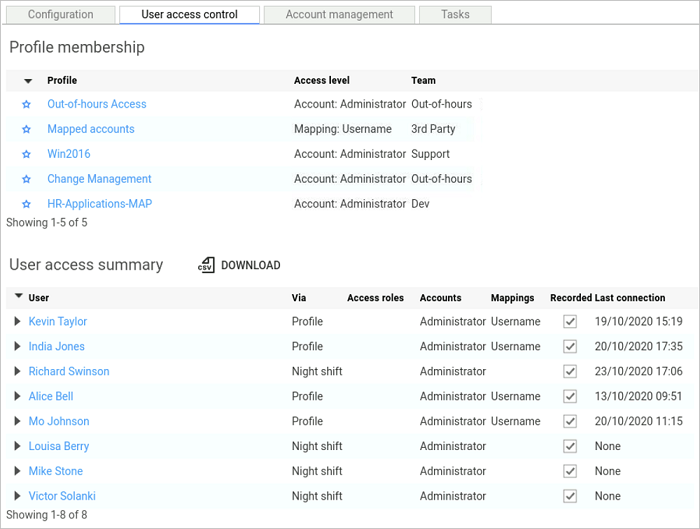
User access control tab
The User access control tab allows you to:
-
View all the profiles the device belongs to. The link between a profile and a device is made with a specific permission, representing the level of permission that will be used when a user single sign-on to the device.
-
View all users that have access to the device and their respective permission levels.
The information presented in the user access summary table includes:
| Heading | Description |
|---|---|
 |
Click the arrow to reveal more information. |
| User | The internal name of the user used to reference and log user activity. |
| Via | Indicates if the user has been added directly to the profile or via a user group. |
| Access roles | Indicates the access level granted to the personalised user created on the device, if a role is selected within the Profile. If an Account is selected then this column will be blank. |
| Accounts | Indicates the account to be used when users single sign-on onto the device. Only accounts which have a state of Known or higher on the Account management page, will be made available when the device is added to a profile. If an Access role is selected then this column will be blank. |
| Recorded | Relates to Privileged Session Recording and if ticked, indicates that a user’s session to the device will be recorded. See Privileged Session Management. |
| Last connection | Timestamp of when the user last single sign-on to the device. |
Account management tab
The information presented on this tab will differ depending on whether the device has been provisioned as a local device, a device using an Active Directory or a static vault.
Device provisioned with a local device account
Example of the Account management tab for a device provisioned with a local device account:
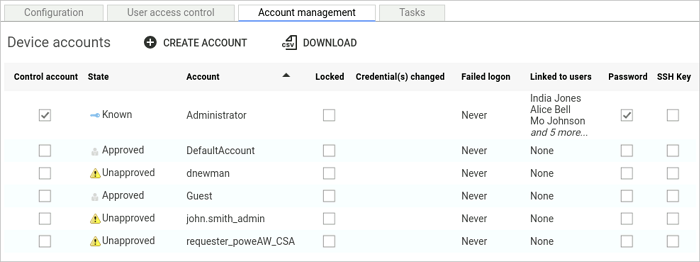
Lists all the accounts that exist on the device.
Device provisioned with an Active Directory account source
Example of the Account management tab for a device provisioned with an Active Directory account source:
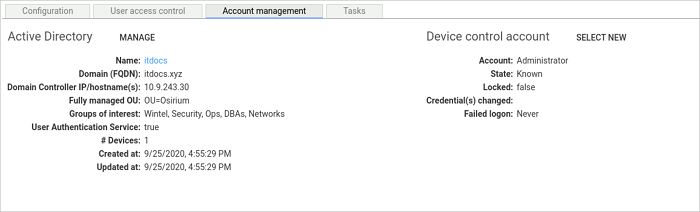
Contains the following details:
-
Active Directory section: provides details of the User authentication service that is linked to the device and being to authenticate Active Directory accounts.
-
Device control account: details the Active Directory account that is used to communicate and run tasks on the member server.
-
Service accounts: lists any service accounts that are being used by the member server.
Device provisioned with a static vault account source
Example of the Account management tab for a device provisioned with a static vault account source:

Contains the following details:
-
Static vault section: provides details of the Static vault that is linked to the device and being used to authenticate accounts.
-
Device control account: details the static vault account that is used to communicate and run tasks on the device.
For more information relating to accounts see Manage Accounts.
Create a local account on a device
This functionality allows you to create an account for devices with local accounts.
To create an account for a static vault see Creating an Account in the Static Vault.
-
Within the Device detail page, click on the Account management tab.
-
Click on the

CREATE ACCOUNTbutton.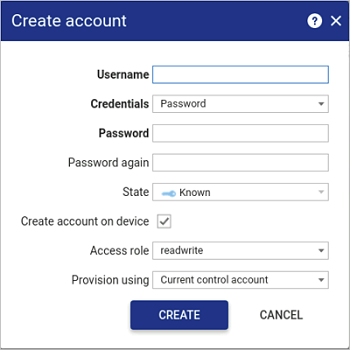
-
Within the Create account window, fill in the following details:
Heading Description Username Enter a valid username for the new user to be created that doesn't already exist on the device. Credentials: Select the authentication method you want to apply against the user. Password and or SSH private key: Depending upon the credential method selected above you will either be asked to enter: - A password.
- An SSH Key.
- Both, password and SSH key.State: Can not be changed. The account state will be set to Known as it will be known and the password stored in the database. NOTE The account state can be changed once it has been created.
Create account on device Choose whether the account should be created on the device If
 enabled you will be prompted to select the Access role and the account to provision the user
enabled you will be prompted to select the Access role and the account to provision the user -
Click
CREATE. The account will be queued for creation. See the System Queue.
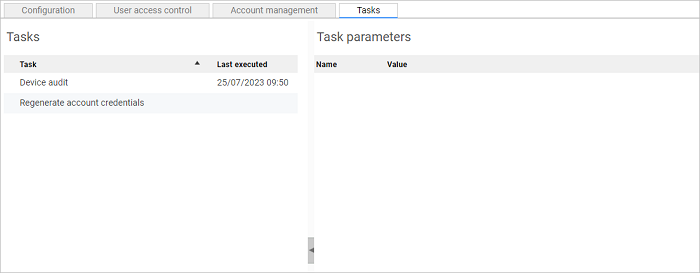
Tasks tab
The Tasks section lists all the System tasks that can be scheduled to run on the device through profiles.
Migrating a template
Provisioned devices can easily be upgraded to a newer version of a device template by using the template migration functionality. You can only migrate the template of a device which is currently enabled.
The updated device template must be uploaded through the Template library page before it can be used. See Uploading the Templates.
To migrate a device template:
-
On the Manage devices page, right-click an individual device (or press CTRL and click multiple devices using the same template) and then click
Migrate template. -
In the Migrate template window, select the new template you want to migrate the device to. Only templates that are compatible with the device will be listed.
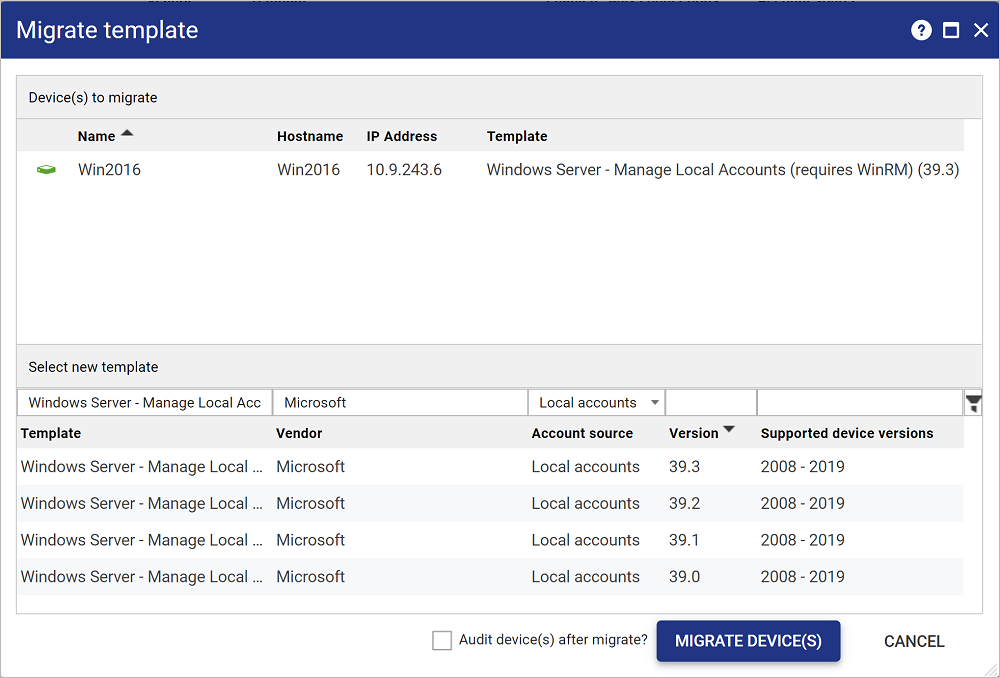
-
Click
MIGRATE DEVICE(S).During the template migration:
- Existing DTPDs (Device Template Parameter Definitions) are checked and either updated or removed.
- The MigrateDevice task is run to migrate the device to the selected template.
- The DeviceAudit task is run to audit information and update the Inventory report and device parameter values.
Note
It is not possible to migrate a device from a Windows Domain template to a Windows Standalone template or from a Windows Standalone template to a Windows Domain template.
Trigger Audit
The 
TRIGGER AUDIT button audits both the device accounts as well as the information presented in the Inventory report.
Reprovision a device
If a device is having issues and is in an unknown state then you can use the REPROVISION button to correctly configure the device.
Editing a device
See Common Interface Functions section for inline editing.
 Device has been successfully provisioned but not yet polled.
Device has been successfully provisioned but not yet polled.  Raised when a task run on the device fails. Look on the Device detail page > Recent system queue or the System queue for failed tasks against the device.
Raised when a task run on the device fails. Look on the Device detail page > Recent system queue or the System queue for failed tasks against the device.  Polling has failed. The Monitor Devices system task has failed to communicate with at least one of the devices available access methods. Therefore, some or all of the device tools may be unavailable.
Polling has failed. The Monitor Devices system task has failed to communicate with at least one of the devices available access methods. Therefore, some or all of the device tools may be unavailable. This device is not managed by Osirium PAM but the username/password are saved within Osirium PAM. The only tool available to device is Reveal Credentials.
This device is not managed by Osirium PAM but the username/password are saved within Osirium PAM. The only tool available to device is Reveal Credentials. unchecked then the device access has been disabled for all users. The device will no longer be available to the user. But the device will NOT be removed from any profiles.
unchecked then the device access has been disabled for all users. The device will no longer be available to the user. But the device will NOT be removed from any profiles.